TR-369 Explained
USP TR-369 is an essential technical standard that reports how application layer protocols in networks along with the data models are used for managing connected consumer devices remotely. One goal behind this specification was to provide easier access from anywhere in any situation without needing express permission every time you want something done, which gives users greater control over what happens with their information when they’re not physically present at home or work respectively – it also simplifies matters greatly on both sides!
To Understand TR-369, We Must Explore TR-069
This is the story of how a group effort to provide remote management for cable modem connections led eventually into something much more. In 2004, when Broadband Forum came up with CPE WAN Management Protocol (CWMP), also called TR-069 after its technical specification had been approved that year – it was the perfect solution for those who needed access but didn’t have enough bandwidth on their own home computers or even be able to use these devices if they did because there weren’t many people owning such equipment back then! The output should show some interest by including dates alongside relevant information; readers want both now vs then since things have changed so.
With the TR-069 specification allowing for multiple connections between an ACS server (autoconfiguration server) and customer premise equipment (CPE), this made sense when devices needed to be manageable by multiple end users because each user would have their own way of accessing data on these hosts. However – as time went on with all sortsa connected gadgets taking up space in our homes or offices–this may no longer cut out enough resources if you’re trying give people easy access from wherever they are without having too many steps involved!.
So what changed with TR-369?
TR-069 was a success in its initial implementation, but as the years went by and we saw more smart device ubiquity it became clear that this specification needed an upgrade. TR 369 caused confusion sometimes called “next generation” because they wanted to create an interoperability protocol while ensuring compatibility between providers; two things which can lead one down rabbit hole if not done correctly (or at least with enough forethought).
TR-369 is a ground breaking protocol that will change the way we think about smart appliances. It gives end users access to these devices and makes them easier for everyone, but it also offers incredible value as service providers can outsource WiFi network management in order offer their own services at least partly through this technology!
So, what does TR-369 do?
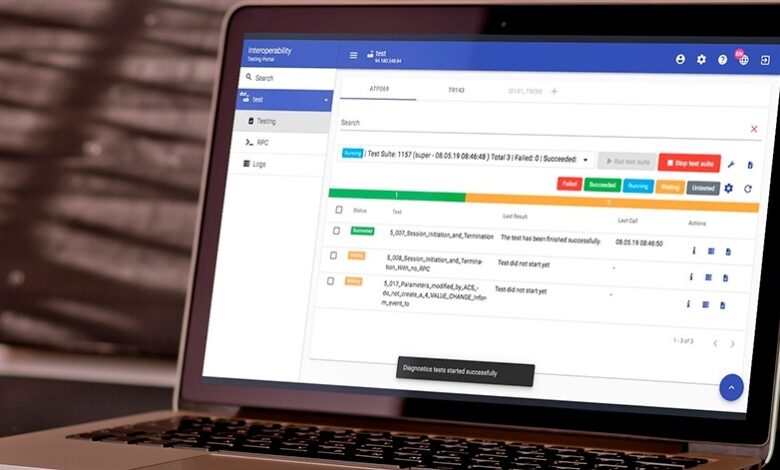
It may be better for TR-369 specialists, and IoT device experts Axiros to explain this than us.
- Lifecycle Management of connected residential devices (service provisioning, device authentication, device configuration)
- Device Upgradability for firmware updates, security patches and software extensions
- Bringing newly installed or purchased devices Into Service
- Status Monitoring and Alert Management of connected devices, services, and home network links
- QoS and QoE Monitoring of home ecosystem service parameters
(reference from: https://www.axiros.com/knowledge-base/usp-tr-369)
Is TR-369 Secure?
TR-369 offers an unparalleled level of security. The message is coaked in encryption records which can be sent over TLS, ensuring its integrity and confidentiality while it travels along pathways throughout your network or even within itself if necessary! Additionally you have options for how to protect yourself: either use Websockets HTTPS connection so nothing malicious slips through undetected; on top there’s CoAP – DTLS (distributed transactions over messaging protocol), where each transaction has three layers protecting them from tampering during transmission.
Multi-Controller Architecture
TR-369 will change the face of security operations by giving controllers unprecedented control over agents. This one large, connected ecosystem enables a never before seen level of flexibility that opens up new stealth tactics and possibilities for attacks on networks both internal as well external to an enterprise.
A person can be manipulated through multiple devices which may include service providers’ operational centers or 3rd party application vendors controlling them directly; there is even potential involvement from local area network gateway nodes facing onto LANS–the latter being able candidates if you’re looking out long enough.
When giving monitoring control to the end user, who wants see a report of connected hosts without any interference from service providers that have access rights for upgrading firmware on their devices in networks deployed by those customers; agents may limit what controllers are able do so it’s impossible for them accidentally mess with important configurations like clock speed or processor type.